AlternativeFreePress.come
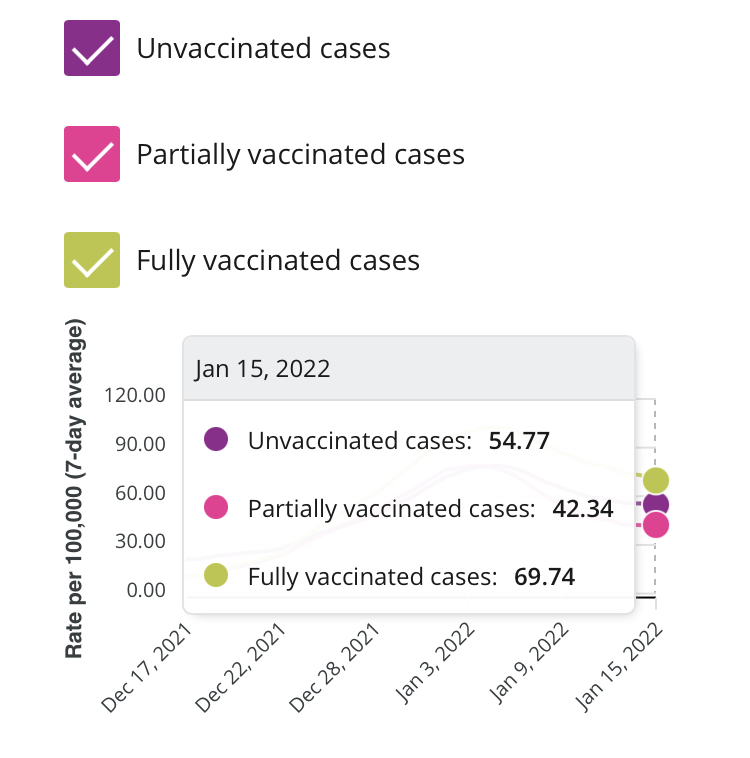
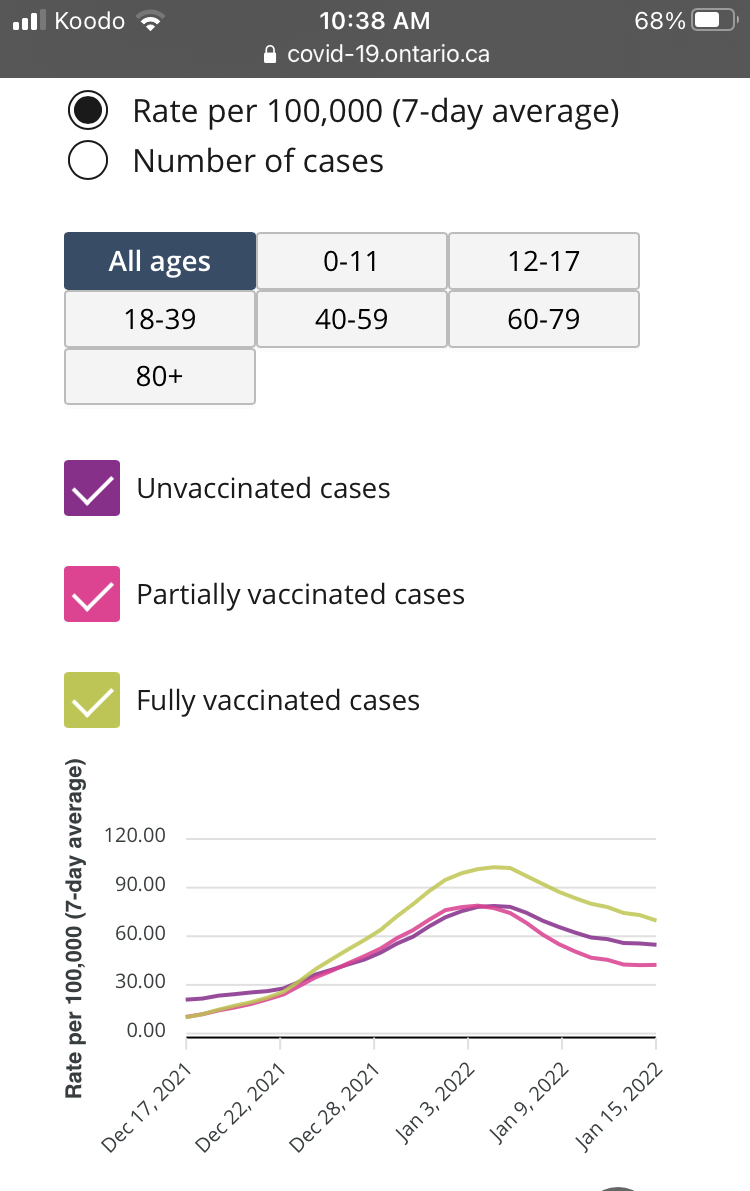
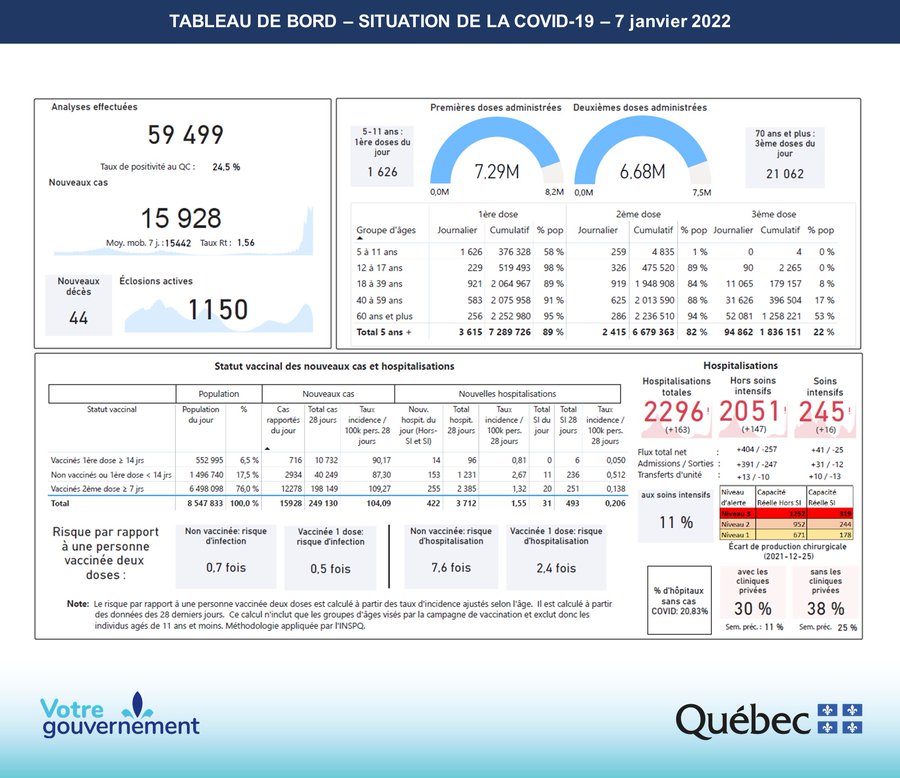
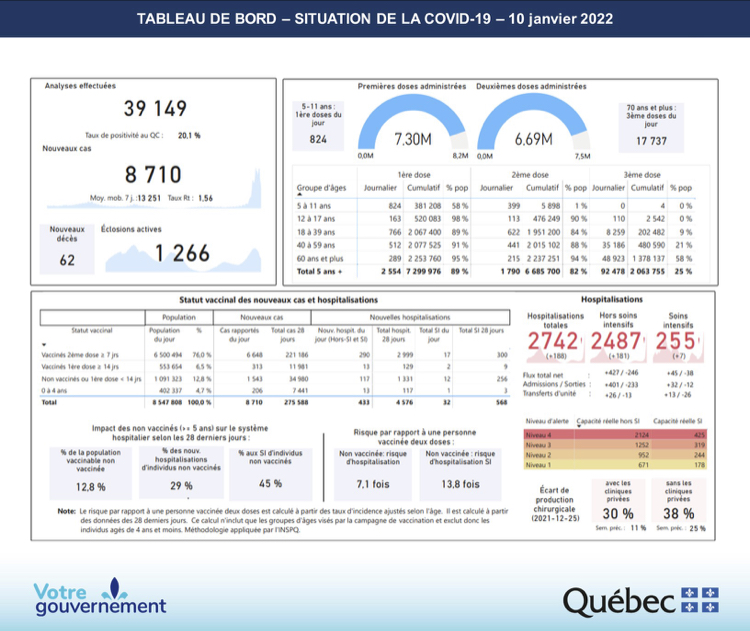
Vaccinated elderly people in British Columbia are being hospitalized at a much higher rate than unvaccinated people. According to this chart from the BCCDC, people over 70 with 2 doses are hospitalized at a rate 80x higher than unvaccinated over 70. (Editor’s note: It seems possible this is an error with ZERO unvaccinated over 70 in hospital, however they have yet to correct it if it is)
The data also shows that boosted individuals make up a whopping 44% of deaths, while only making up 18% of the population. Notably, this is a higher increase than the unvaccinated. While the unvaccinated proportion of death is under double the unvaccinated population, the boosted proportion of death is well over double the boosted population. (Editor’s note: these number have been changing rapidly, this is just a snapshot in time)